I have been watching the Java Patch Cycle for a little while now. And, I am starting to get a little concerned.
 Only approximately 5% of installations are using version 1.7.17 and therefore are secure.
Only approximately 5% of installations are using version 1.7.17 and therefore are secure.
I have always struggled with the non-Microsoft update for desktops and servers due to the additional "tier" of update processes required. Microsoft updates it's applications and OS (server and desktop) in a pretty mature and robust manner. This is no great thing, as they have a few years to get pretty slick at updating desktop and Microsoft applications for a while now. However, middle-ware applications like Java are not handled by the Microsoft update infrastructure and need an extra process and usually additional technology to complete the deployment and update process.
In addition, JAVA is a "self-warning" update process that let's you know an update is required for download and install as opposed to the "self-updating" nature of applications like Chrome.
And, this current update approach does NOT appear to be working. A recent report from Websense indicates that JAVA is a major security concern we now have to recognize the potential for numerous Zero-day attacks and that JAVA exploits are now a major tool for cybercriminals. Websense has published the following diagram demonstrating the number of different versions of JAVA expressed through browsers - Note the tiny percentage running the latest version.
 Only approximately 5% of installations are using version 1.7.17 and therefore are secure.
Only approximately 5% of installations are using version 1.7.17 and therefore are secure.
Charles Renert, vice president of Websense Security Labs comments,
"Patch management can be a complicated process for an organization, especially those with remote workers," There are a number of factors at play: a mobile workforce is hard to patch; Java has a cross-platform footprint; and Java updates independently from the vulnerable apps, such as browsers, that use it."
I seem to be running two versions, as you can see by my Add/Remove Control Panel applet
Not sure that this a good thing...
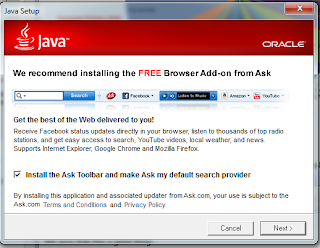
And, we are getting into slight rant territory here - do we really have to "opt-out" out of setting ASK as our default search engine for every update. Here is a quick snippet from the installation process.
ASK? Really? Are they still in business? Maybe their search provider business partners are an indication of just how relevant JAVA is today compared with the capabilities offered by the JSON tool-kits....
Even worse, after installing the latest update, I received an error message indicating the that security certificate had been revoked... Hmmpf!
References:
Unpatched Java Versions Remain Widely Used: Report
Java-based attacks remain at large, researchers say
How are Java attacks getting through?

No comments:
Post a Comment